governance & service management
ITOM can now realise the promises of ITSM
Gil Regev, Olivier Hayard & Alain Geerts · October 08, 2024
Gil Regev, Olivier Hayard & Alain Geerts · October 08, 2024
The ever increasing digitalisation of our service infrastructure makes us dependent on a myriad of IT components for the accomplishment of tasks from the most mundane to the most mission critical. From buying bread at the local bakery to being treated in an emergency room through the purchasing of a train ticket, we have become sensitive to the most minor of service disturbances. Who wants to miss their train and therefore their all important meeting just because the smartphone app is now unable to complete the financial transaction? Who wants to get a repeat surgery because their patient data is just now unavailable in the operation block?
All organizations, small to large, private to public, are now concerned by these service guarantees that must match their stakeholders expectation. Not only has the bar been raised on the expectations side, the technology stack, or rather, network, has seen a comparable increase in complexity. The term ITOM was coined a few years ago to designate this backbone that maintains the IT Service Management frontend (ITSM) where stakeholders expectations are met and value is created.
You might wonder why a new term is needed. Don’t we have enough concepts with ITSM, DevOPS, AIOps, SecOps etc? The simple answer is that IT vendors needed an all-encompassing term to designate the many organizational and technological parts that together enable ITSM. ServiceNow, one of the ITSM market leaders [1], lists the following apps and capabilities for its ITOM module [2]: Discovery, Service Mapping, Certificate management, Firewall Audit and reporting, Service Graph Connectors, Configuration Management Database (CMDB), Agent Client Connector, Event Management, Metric Intelligence, Health Log Analytics, Cloud Accelerate.
DevOps, AIOps, SecOps and the apps and capabilities of a vendor’s module are the components of ITOM. The simplified and global picture is therefore of ITSM as stakeholders-facing (customers, suppliers, employees) and ITOM as the hidden infrastructure (or backbone) that enables it. See Exhibit 1.
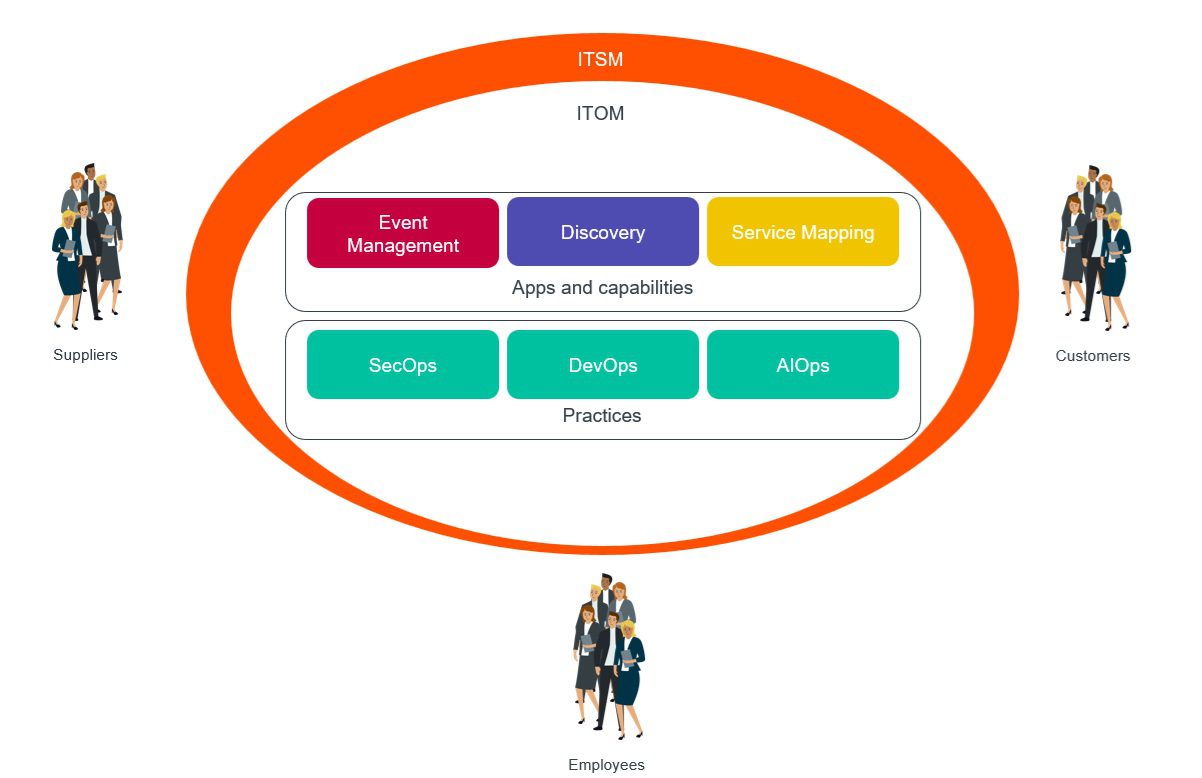
Looking at this picture you might think that this is yet another bag of things with a name, but there’s more to it than that. ITOM is all about the integration of the apps, capabilities and practices, with AI as a main enabler. To understand the possibilities offered by this integration let us consider a few examples.
How can you efficiently create and maintain a trustable CMDB that is both correct and complete? With the Discovery module you can identify the state of your CIs (the territory) and to compare it with what it should look like (the map). The Service Mapping module enables you to automatically register the dependencies between your services with your CIs. It also has semi-automatic capabilities that suggest possible dependencies that are then validated manually. Some other dependencies must be made completely manually. Service Mapping can then propose automatic tracing of the route from an entry point (a user request, a URL, an API). Your CMDB is likely spread across multiple applications (e.g. monitoring tools such as Dynatrace, or vulnerability assessment tools such as Tenable) each using different CI identifiers. You can use Correlation IDs to identify a given CI across the applications in which it is referenced.
The integration of authoritative sources (CMDB) provides you with the CIs that are to be monitored for automatic incident record creation with respect to events such as lack of drive space or memory in a VM. Once an incident occurs, what help can you get for investigating it? Event Management integrated with your service graph, which in turn is dependent on Service Mapping and CMDB, can help you to determine the most probable root cause so that the relevant people are alerted. This helps you to avoid exhausting your experts with incidents that do not concern them and getting them to work on those that are the most urgent and important. Problem Management is also about being proactive in preventing incidents. With ITOM you can provision the resources needed for your services integrating your Service Graph and CMDB with VMWare for proper configuration. You can then automatically monitor and configure the VMs through VMWare, e.g. increase memory or processors in response demand spike.
To maintain a secure IT landscape, even for a small or medium size park, you need automatic patching, updates, as well as vulnerability, obsolescence and intrusion detection (e.g. Tenable). Some of these features are provided by the vendors of individual components, such as OS and drivers, but what about forward looking, proactive management? What about managing the lifecycle of your security certificates and licenses so that they don’t expire and create service disruptions? What about the management of interactions that can bring down a sensitive service at the worst possible moment? How would you guard yourself against a critical VM that has decided to update just at the most congested weekend of the year? If a zero day vulnerability affects your software or hardware, you want to be alerted immediately and forcibly so as to possibly change your change request priorities. But you don’t want to be alerted by even zero day vulnerabilities if your IT park is not affected by it. You don’t want to be woken up every other night by an alert just to discover that it affects software that you don’t have. ITOM helps you by integrating the capabilities of Discovery, Service Mapping, Certificate Management, Firewall Audit and CMDB to identify threats and intelligently filter them by their potential impact on your service portfolio. The examples above are drawn from our experience helping IT departments to deliver this value to their stakeholders.
The promise of ITOM is that the integration and automation of its capabilities with the use of modern development and operations processes and tools can help you to deliver the value you always expected from your ITSM initiatives.
Footnotes:
[1] Acknowledged as such by Gartner and Forrester Research
[2] https://www.servicenow.com/products/it-operations-management.html
| Cookie | Duration | Description |
|---|---|---|
| __hssrc | Session | This cookie is set by Hubspot whenever it changes the session cookie. The __hssrc cookie set to 1 indicates that the user has restarted the browser, and if the cookie does not exist, it is assumed to be a new session. |
| _GRECAPTCHA | 5 months 27 days | This cookie is set by the Google recaptcha service to identify bots to protect the website against malicious spam attacks. |
| cookielawinfo-checkbox-advertisement | 1 year | Set by the GDPR Cookie Consent plugin, this cookie is used to record the user consent for the cookies in the "Advertisement" category . |
| cookielawinfo-checkbox-analytics | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Analytics". |
| cookielawinfo-checkbox-functional | 11 months | The cookie is set by GDPR cookie consent to record the user consent for the cookies in the category "Functional". |
| cookielawinfo-checkbox-necessary | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookies is used to store the user consent for the cookies in the category "Necessary". |
| cookielawinfo-checkbox-others | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Other. |
| cookielawinfo-checkbox-performance | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Performance". |
| CookieLawInfoConsent | 1 year | CookieYes sets this cookie to record the default button state of the corresponding category and the status of CCPA. It works only in coordination with the primary cookie. |
| JSESSIONID | session | New Relic uses this cookie to store a session identifier so that New Relic can monitor session counts for an application. |
| viewed_cookie_policy | 11 months | The cookie is set by the GDPR Cookie Consent plugin and is used to store whether or not user has consented to the use of cookies. It does not store any personal data. |
| Cookie | Duration | Description |
|---|---|---|
| __cf_bm | 30 minutes | This cookie, set by Cloudflare, is used to support Cloudflare Bot Management. |
| __hssc | 30 minutes | HubSpot sets this cookie to keep track of sessions and to determine if HubSpot should increment the session number and timestamps in the __hstc cookie. |
| Cookie | Duration | Description |
|---|---|---|
| __hstc | 1 year 24 days | This is the main cookie set by Hubspot, for tracking visitors. It contains the domain, initial timestamp (first visit), last timestamp (last visit), current timestamp (this visit), and session number (increments for each subsequent session). |
| _ga | 2 years | The _ga cookie, installed by Google Analytics, calculates visitor, session and campaign data and also keeps track of site usage for the site's analytics report. The cookie stores information anonymously and assigns a randomly generated number to recognize unique visitors. |
| _ga_* | 1 year 1 month 4 days | Google Analytics sets this cookie to store and count page views. |
| _ga_JYCPSB48B8 | 2 years | This cookie is installed by Google Analytics. |
| _gat_gtag_UA_* | 1 minute | Google Analytics sets this cookie to store a unique user ID. |
| _gid | 1 day | Google Analytics sets this cookie to store information on how visitors use a website while also creating an analytics report of the website's performance. Some of the collected data includes the number of visitors, their source, and the pages they visit anonymously. |
| CONSENT | 16 years 2 months 25 days 10 hours | YouTube sets this cookie via embedded youtube-videos and registers anonymous statistical data. |
| hubspotutk | 1 year 24 days | This cookie is used by HubSpot to keep track of the visitors to the website. This cookie is passed to Hubspot on form submission and used when deduplicating contacts. |
| Cookie | Duration | Description |
|---|---|---|
| IDE | 1 year 24 days | Google DoubleClick IDE cookies are used to store information about how the user uses the website to present them with relevant ads and according to the user profile. |
| test_cookie | 15 minutes | The test_cookie is set by doubleclick.net and is used to determine if the user's browser supports cookies. |
| VISITOR_INFO1_LIVE | 5 months 27 days | A cookie set by YouTube to measure bandwidth that determines whether the user gets the new or old player interface. |
| YSC | Session | YSC cookie is set by Youtube and is used to track the views of embedded videos on Youtube pages. |
| yt-remote-connected-devices | never | YouTube sets this cookie to store the user's video preferences using embedded YouTube videos. |
| yt-remote-device-id | never | YouTube sets this cookie to store the user's video preferences using embedded YouTube videos. |
| Cookie | Duration | Description |
|---|---|---|
| VISITOR_PRIVACY_METADATA | 5 months 27 days | Description is currently not available. |